How to configure IGMP Snooping on Omada switches for hotel IPTV scenario
Contents
Introduction
Multicast is one of the key technologies used in hotel IPTV services. Any Omada SG2xxx series and above support a full set of multicast features, including IGMP Snooping, IGMP Querier, Drop Unknown Multicast, and Fast Leave. These capabilities enable the switches to deliver a stable IPTV service for hotels of any scale. Since Omada Controller version 6.0, the configuration of multicast IPTV has become even easier through an intuitive GUI. It offers scenario-oriented settings tailored for hotel IPTV applications, making IPTV deployment simple and user-friendly. With the Omada SDN network, you can also benefit from centralized management, cloud access, and Zero-Touch Provisioning (ZTP), delivering additional value to IPTV integrators, IT system integrators, and managed service providers (MSP). In this guide, we will demonstrate the best practice configuration for hotel multicast IPTV using the Omada Controller.
Requirements
- All Omada Switches except Agile Switches
- The multicast sources and multicast clients, like TVs
- Omada Controller v6.0 or above
Configuration
General Principals
To help you better understand the configurations, we will provide some simple background explanations. If you are already familiar with these concepts, you can skip this section.
1. IGMP Snooping & IGMP Querier
Without IGMP Snooping, multicast traffic is transmitted through the switch like broadcast traffic, which increases bandwidth usage and degrades network performance. IGMP Snooping helps generate a multicast forwarding table using IGMP report and querier packets, ensuring that multicast packets are only sent to the intended ports. Without an IGMP Querier, the multicast forwarding table can age out. The IGMP Querier periodically sends IGMP Querier packets, allowing the switch to maintain the multicast forwarding table. It is important to note that there must be exactly one IGMP Querier in the multicast network there must be exactly one IGMP Querier in the multicast network there must be exactly one IGMP Querier in the multicast network there must be exactly one IGMP Querier in the multicast network.
2. Drop-unknown multicast
It is highly recommended to enable this feature because most IPTV streamers indiscriminately send traffic to all channels. If the Drop-Unknown Multicast feature is not enabled, the network can become saturated with unnecessary multicast traffic, negatively impacting overall IPTV performance. When Drop-Unknown Multicast is enabled, the switch first checks whether a multicast forwarding entry exists for the group; if not, the switch drops the multicast traffic.
3. Multicast Fast Leave
When the switch receives an IGMP Leave packet from a port, by default it does not immediately remove the port from the multicast forwarding table. Instead, the port is removed after the aging time expires. With the Fast Leave feature enabled, the switch removes the port from the multicast forwarding table as soon as it receives the IGMP Leave packet. Fast Leave ensures faster and smoother channel switching and reduces unnecessary multicast traffic on the network. It is recommended to enable this feature for hotel IPTV deployments.
Fast Leave should only be enabled on ports with a single TV/STB connected.
Do not enable it on ports cascaded with other switches or APs, because enabling it in such scenarios may cause channel switching on one TV to freeze the video on another TV connected to the same switch/AP behind that port. Taking the following topology as an example:
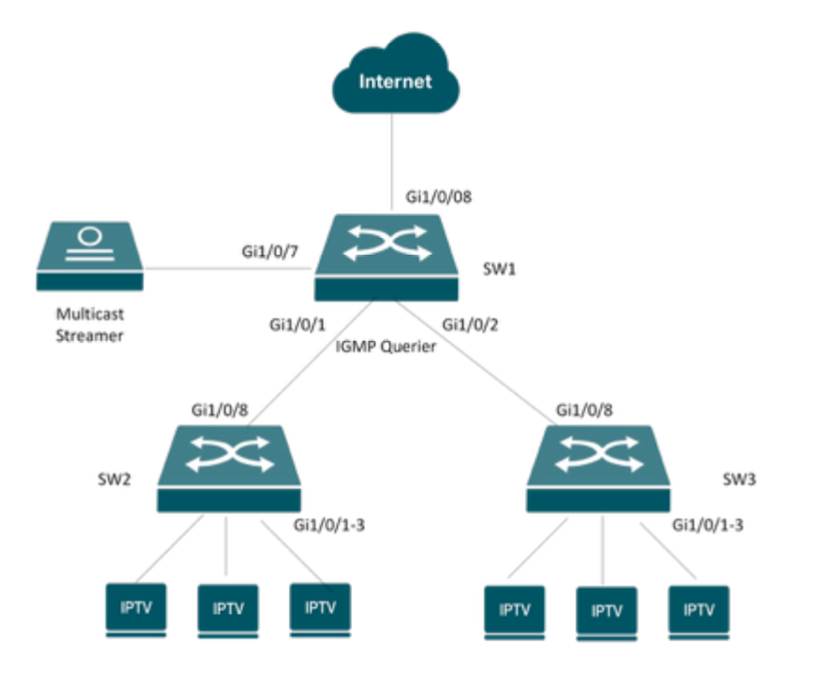
For SW1, you should not enable Fast Leave on the downlink ports, because these ports are connected to other switches where multiple STBs are connected. For example, if Fast Leave is enabled on port Gi1/0/1, when this port receives an IGMP Leave packet from the downlinks, SW1 will immediately remove the port from the multicast forwarding table. This may cause channel freezing issues for other STBs on the downlink that are watching the same channel.
4. Report Suppression (Optional)
When the switch receives multiple IGMP Report packets from multiple STBs requesting to join the same source group within an IGMP Querier interval, the switch forwards only the first report packet to the upstream network. This reduces unnecessary report traffic on the network. It is recommended to enable this feature on all switches, especially in large IPTV deployments.
5. IGMP Router Port (Optional)
The router port is the port through which multicast traffic is forwarded and to which IGMP Report/Leave packets are sent to on a switch. The switch can automatically select the router port based on where it receives IGMP Report packets or PIM Hello packets. In most cases, you do not need to configure the router port manually and can rely on the switch’s default settings.
Configuration examples
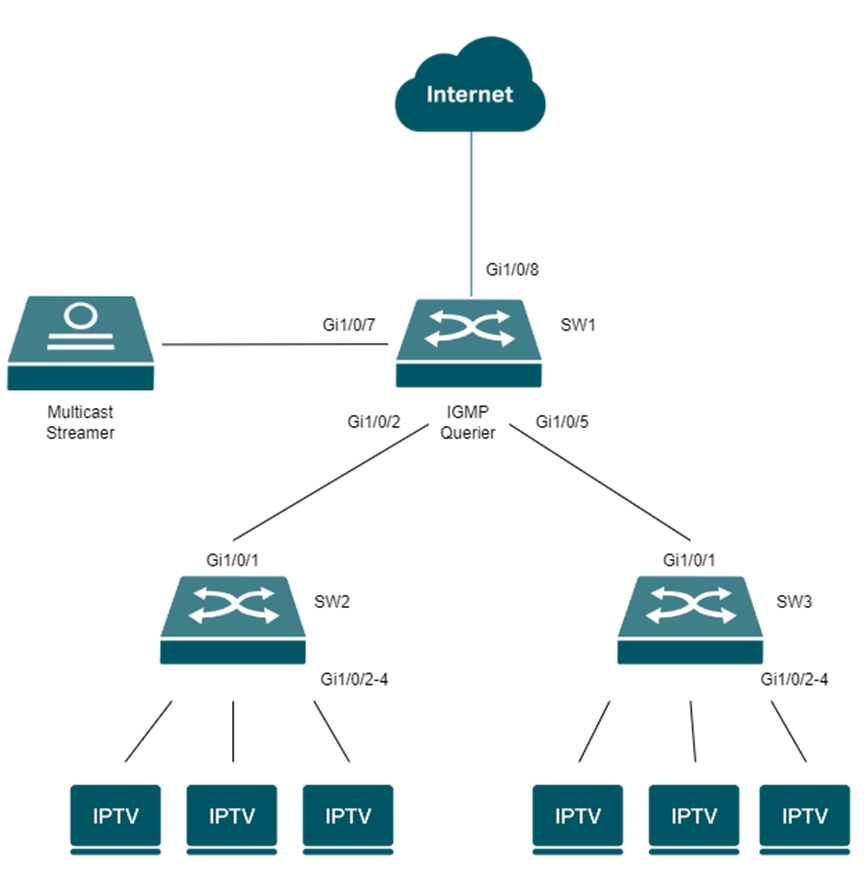
Arrangement: We will use the following network for demostration. The Multicast Streamer is connected to SW1's Gi1/0/7 port. SW1 works as the IGMP Querier. And its Gi1/0/1 and Gi1/0/2 port connect the access switch SW2 and SW3. SW2 and SW3's Gi1/0/1-3 ports connect the IPTV TV/STBs
To ensure stable IPTV service, multicast traffic should be placed on a dedicated VLAN. This prevents interference from other network traffic. If you have switches dedicated to IPTV, you can use the default VLAN 1. In this guide, we will use VLAN 90 as the IPTV VLAN.
|
Purpose |
VLAN |
|
Management VLAN |
VLAN 1(default VLAN) |
|
IPTV VLAN |
VLAN90 |
|
Switch |
Port |
VLAN |
|
SW1 |
Gi1/0/7 |
Access (VLAN 90-untagged; PVID = 90) |
|
SW1 |
Gi1/0/2 Gi1/0/5 |
Trunk (VLAN 1-untag; VLAN 90-tagged; PVID = 1) |
|
SW2 |
Gi1/0/1 |
Trunk (VLAN 1-untagged; VLAN 90-tagged; PVID = 1) |
|
SW2 |
Gi1/0/2-4 |
Access (VLAN 90-untagged; PVID = 90) |
|
SW3 |
Gi1/0/1 |
Trunk (VLAN 1-untagged; VLAN 90-tagged; PVID = 1) |
|
SW3 |
Gi1/0/2-4 |
Access (VLAN 90-untagged; PVID = 90) |
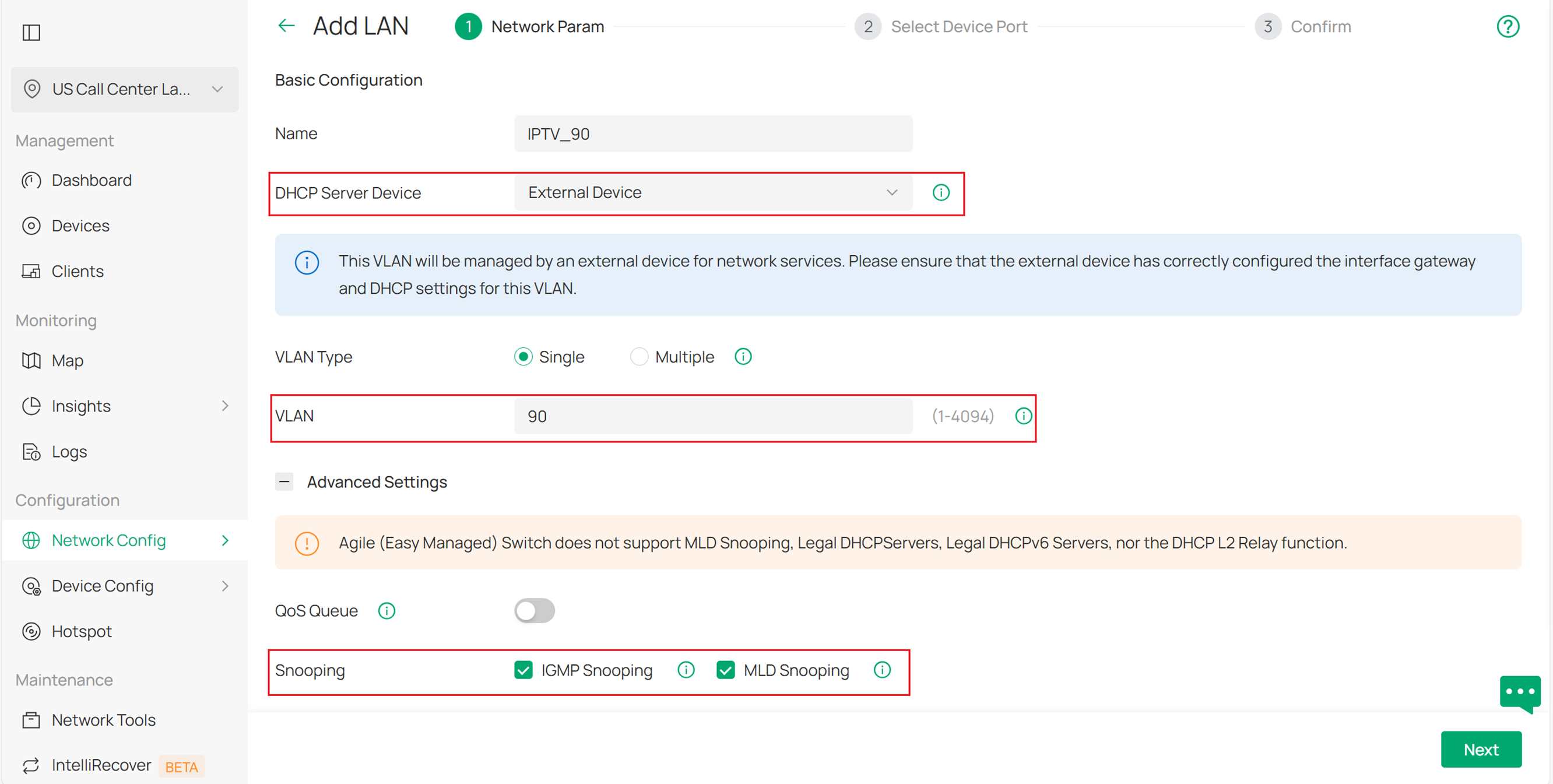
Step 1. Create VLAN for IPTV. Navigate to Site View > Network Config > Network Settings > LAN > VLAN and create VLAN 90 for IPTV as shown below. In our case, we will use a third-party device as the DHCP server, so we select External Device for the DHCP Server Device option. MLD Snooping is used for IPv6 multicast, and it can be enabled at the same time even if IPv6 multicast is not being used in this scenario.
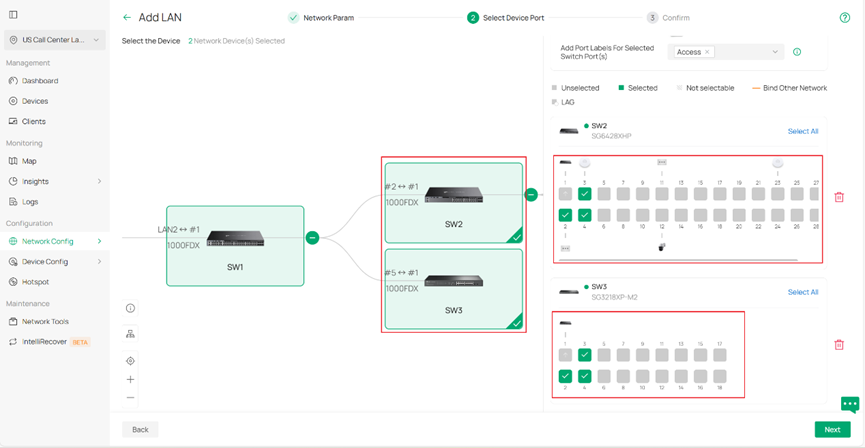
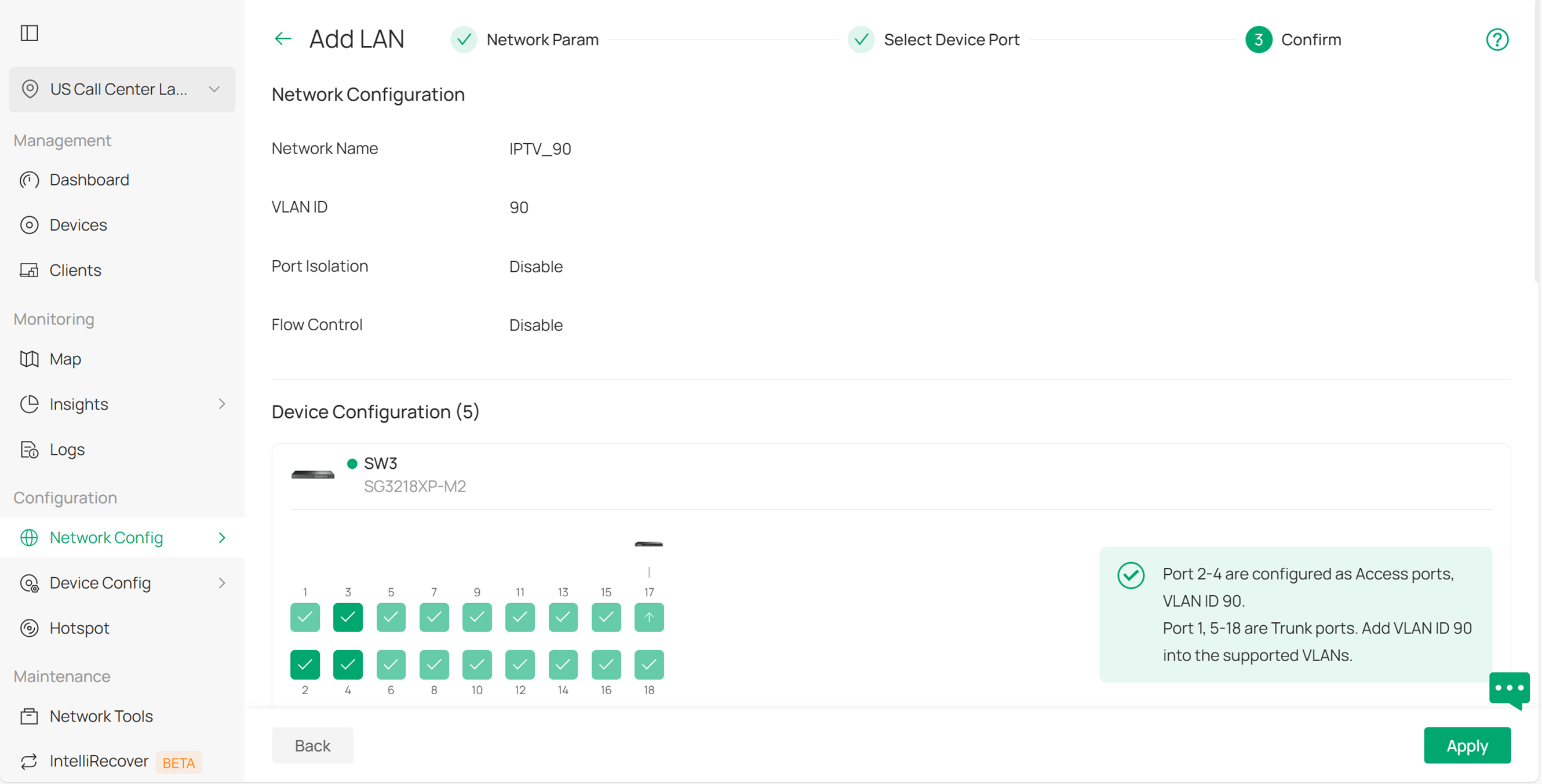
Click Next, and you can select the switches and configure the access ports directly here. In this example, click SW2 and SW3, then select ports 1–3 on both switches. This will configure ports 1–3 on SW2 and SW3 as Access ports for VLAN 90. You do not need to configure the trunk ports manually — the remaining ports will be set as Trunk ports by default. It is recommended to assign Port Labels to these ports so that you can easily identify or modify them later in batch. You can also skip this step and perform these settings after the VLAN is created.
Click Next, it will give a summary of the settings. Click Apply to save.
Step 2. Configure the Multicast Features. Go to Site View > Network Config > Network Settings > LAN > Multicast Snooping, and click Add to create a new configuration. Select VLAN 90 as the Snooping Network and choose IGMP Snooping (v4) as the Protocol. Enable Drop Unknown Multicast, and enable the Querier on the aggregation switch (in this case, SW1) that is closest to the multicast source. Also, enable Report Suppression. You can keep the other settings as default.
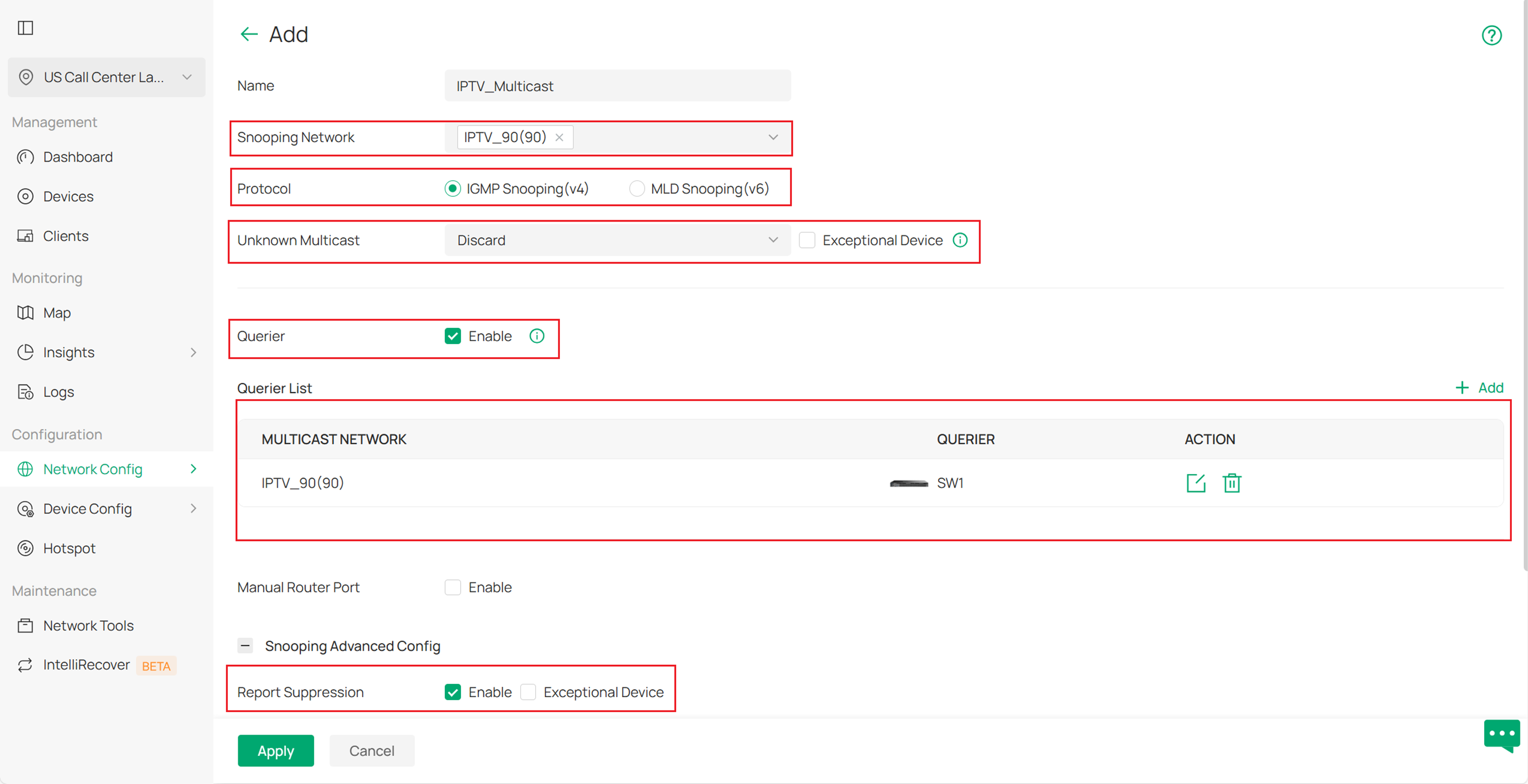
Unknown Multicast: Specify handling method for unidentified multicast packets.
-
Forward: Flood unknown multicast traffic within VLAN.
-
Discard: Drop unknown multicast packets.
-
Router Port First: Forward to router ports (static/dynamic) if available; otherwise flood within VLAN.
Note: Only scenarios where dual stack is running need to consider this limitation.
Within the same network (VLAN), if both IPv4 and IPv6 protocol stacks are operating simultaneously (i.e., IGMP and PIM need to be enabled at the same time), there is a special constraint on how unknown multicast traffic is handled:
If one protocol stack is configured as Router Port First, the other protocol stack must also be configured as Router Port First.
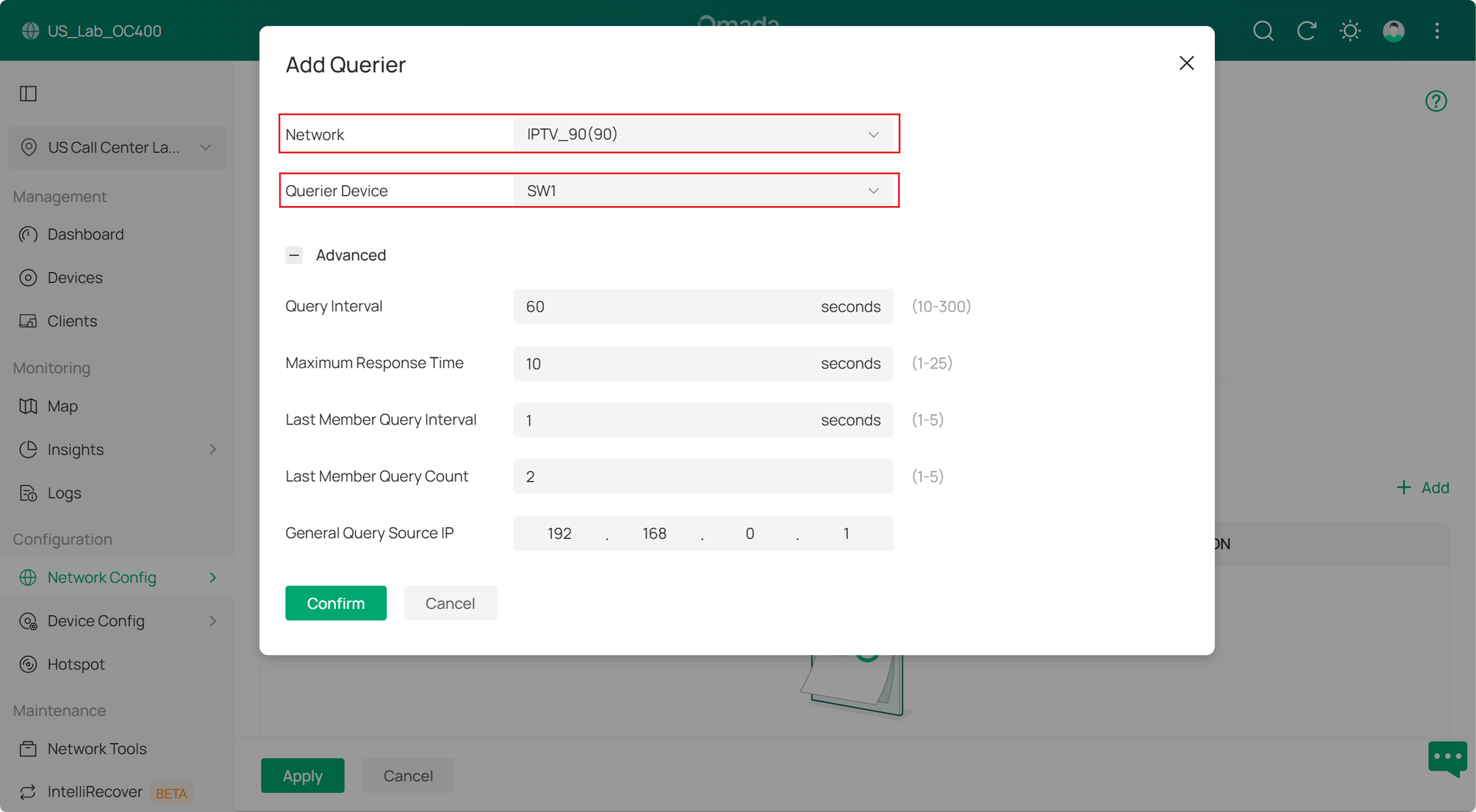
About the Querier settings, we select VLAN 90 and choose the switch that will act as the Querier. You can keep the other settings as the default
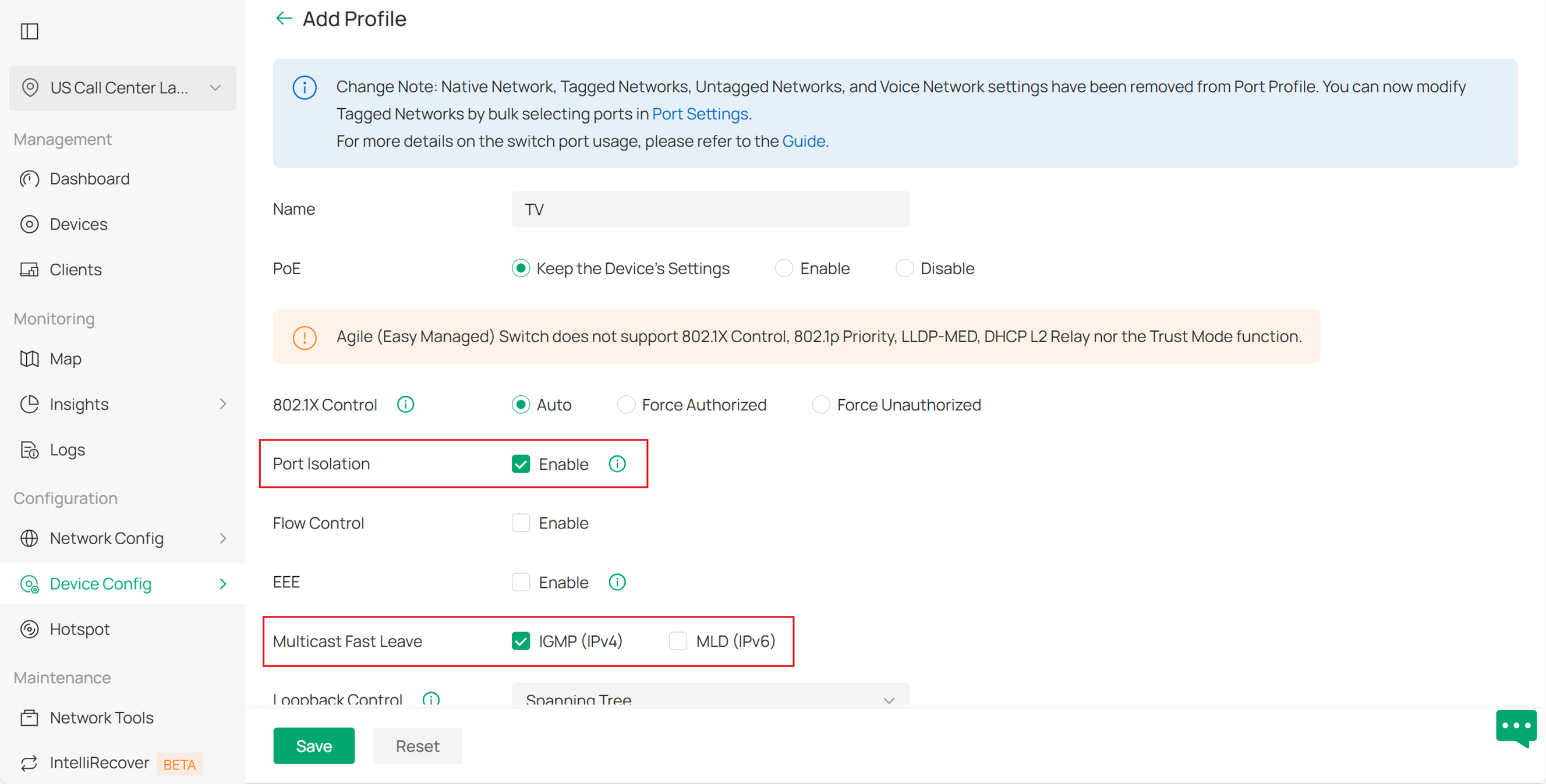
Step 3. Create Port Profile with Fast Leave for TV. Navigate to Site View > Device Config > Switch > Switch Ports > Port Profile, and click Add to create a new port profile.Enable Multicast Fast Leave. If you want to isolate the TVs, you can also enable Port Isolation.You can keep the other settings as default
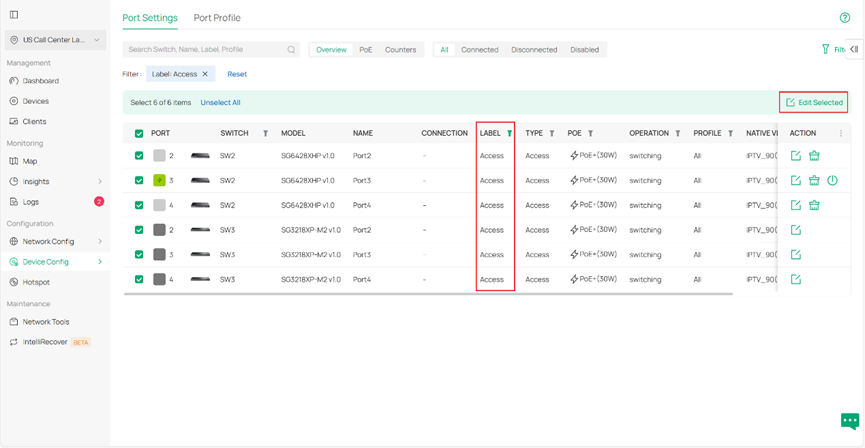
Step 4. Apply the TV port profile to the switch port. Go to Site View > Device Config > Switch > Switch Ports > Port Settings. If you have set up port labels, you can filter the ports by label. Select all the filtered ports, then click Edit Selected in the top-right corner to edit them in batch.
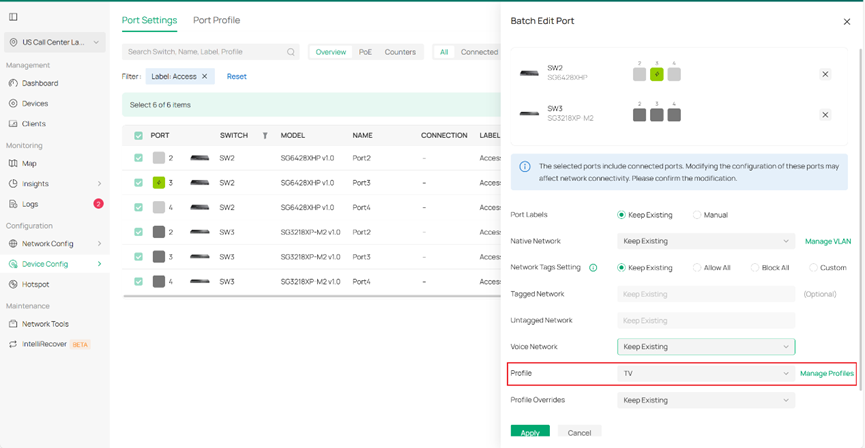
Choose the TV profile you just created, keep the other settings at their defaults, and click Apply to save the changes.
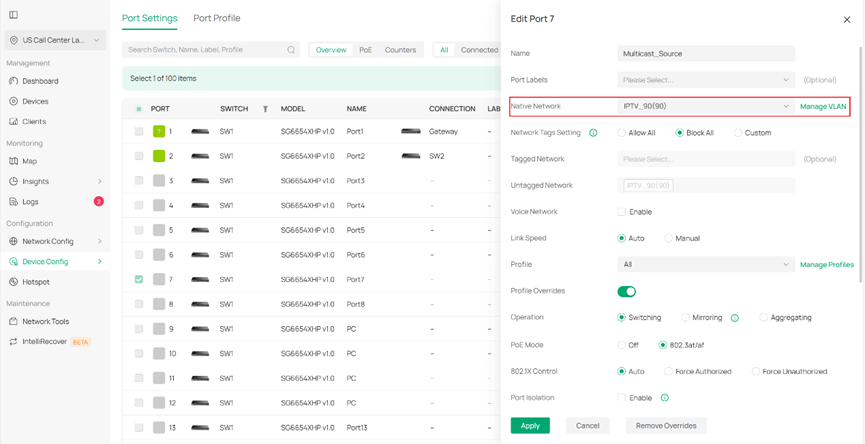
Step 5. Configure the port that connect the multicast source. Configure the port’s VLAN settings (tagged or untagged) according to the multicast source server’s requirements. In this example, we use an Access port on VLAN 90 for the multicast source.
Verification
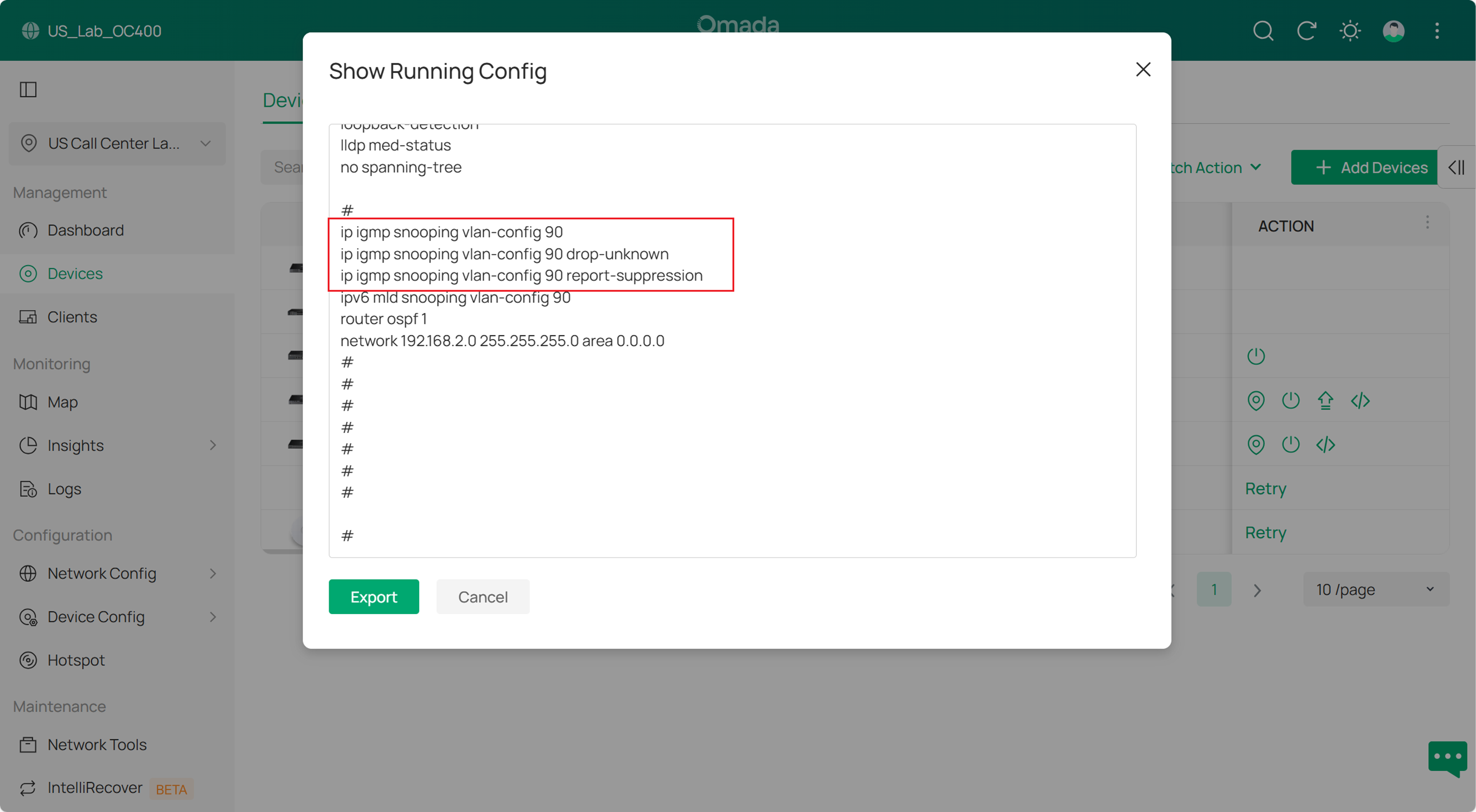
1. You can verify the configuration Verify the configuration Verify the configuration By clicking this icon, you can view the running configuration of the switch to verify whether your settings are correct.
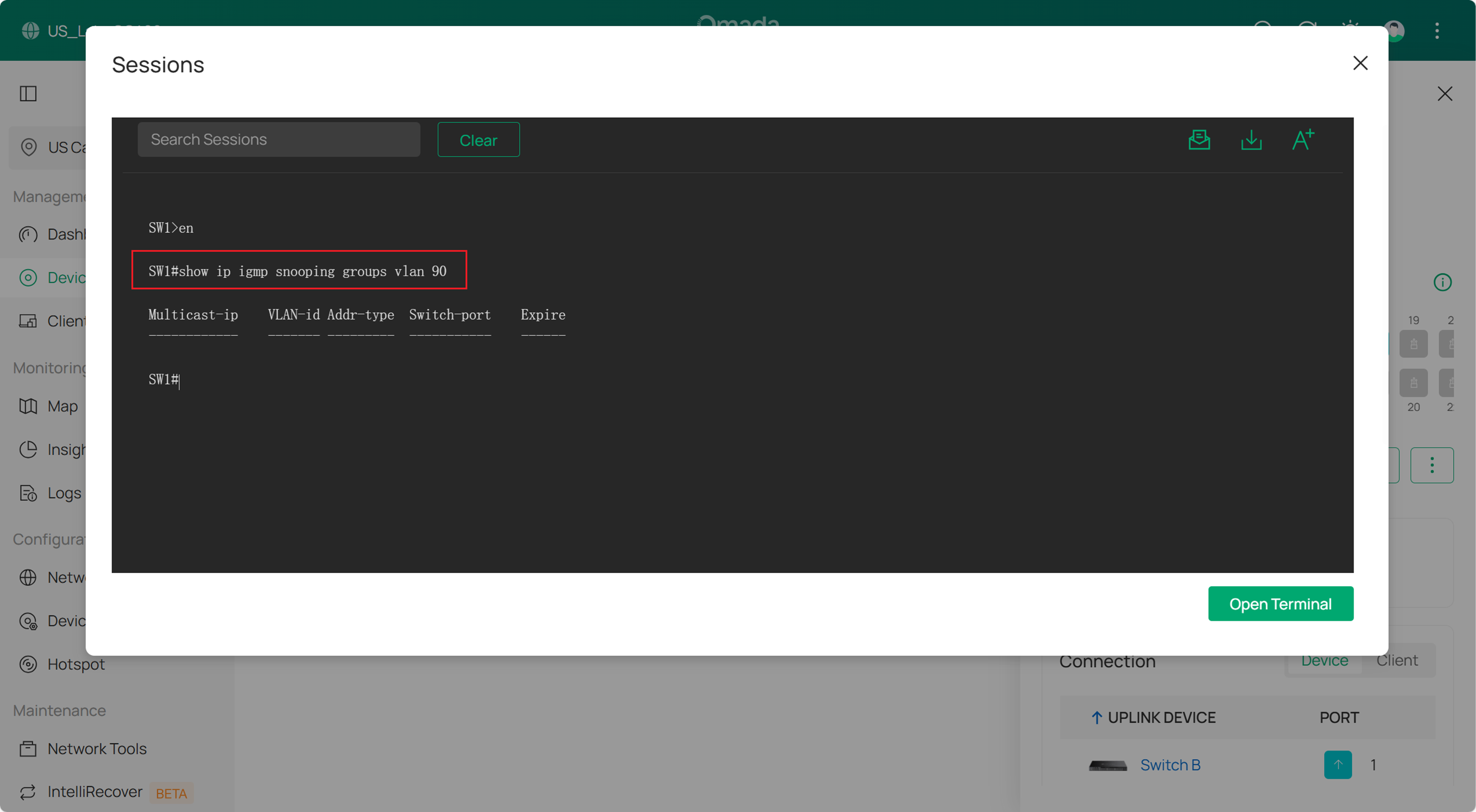
2. Check the multicast group Check the multicast group Check the multicast group Check the multicast group There is currently no GUI display for the multicast group; this will be added in a future update. To check the multicast group, you can use the Device Terminal under Device Config > Tool > Terminal. Use the following command to view the multicast groups on this switch.
Conclusion
You can refer to the above examples and customize your IPTV settings according to your specific needs.
Get to know more details of each function and configuration please go to Download Center to download the manual of your product.







